The cryptosphere today resembles a giant digital graveyard. According to Chainalysis, over 3.7 million BTC are locked in addresses to which access is considered lost forever. The total market value of these assets runs into tens of billions of dollars. Traditionally, it is believed that cracking a private key is a task requiring time exceeding the age of the Universe. However, the Bitcoin Private Key Finder — BTC Hunter project proves that this postulate is only true for perfectly isolated mathematical systems. In the real world of software code, vulnerabilities exist that transform “impossible” searching into a scientifically grounded hunt.
1. The Crisis of Classical Brute Force and the Shift to Heuristics
Classical Brute Force is a “Stone Age” method. It relies on attempting to guess a number in the range from 1 to 2^256. The mathematical probability of success here is negligible. However, modern cryptography operates not only with raw numbers but with the environment of their generation.
BTC Hunter v2.4 utilizes a transition from random search to stochastic analysis and heuristic modeling. Instead of scanning an infinite void, the program focuses on “information noise” zones where the probability of a key appearing is higher due to the design features of the software used to create wallets between 2009 and 2017.
2. The Genesis of Vulnerabilities: Why Does Entropy Fail?
The heart of any wallet is the private key, generated based on entropy (randomness). If entropy is weak, the key becomes predictable. The BTC Hunter program analyzes three critical factors of entropy failure:
- Modulo Bias: The “square peg in a round hole” problem. Many generation algorithms attempt to fit a large random number into the Bitcoin private key range using modulo division. This creates a statistical bias, where certain ranges of numbers appear more frequently than others.
- Temporal Seeding: Thousands of early wallets were generated using system time as a “seed” for the PRNG. This narrows the search space from 2^256 to a few million variants tied to specific seconds in blockchain history.
- Browser Artifacts (V8 & SpiderMonkey): The JavaScript engines that many online wallets relied on had specific implementations of the Math.random() function, possessing predictable patterns in 32-bit and 64-bit systems.
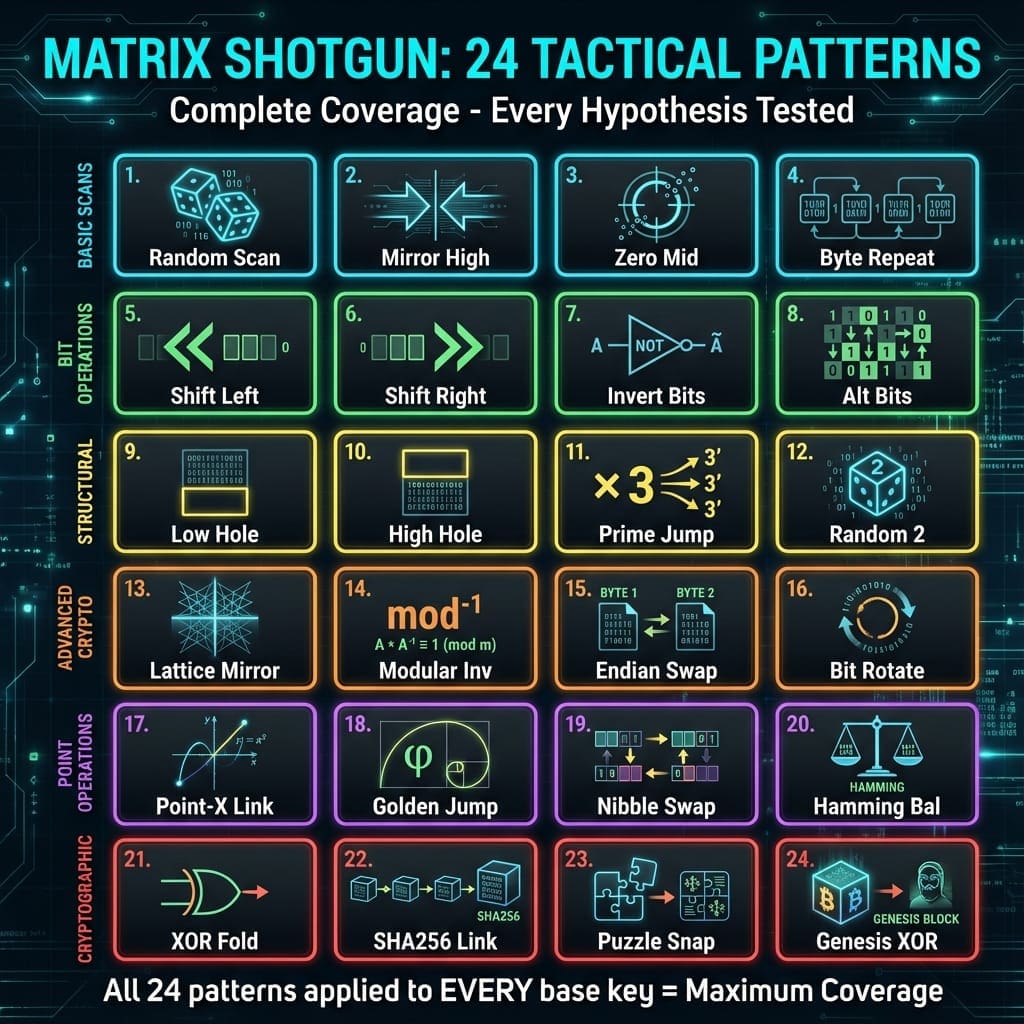
3. Matrix Shotgun Strategy: 24 Tactical Mutation Patterns
The core innovative advantage of BTC Hunter lies in the Matrix Shotgun method. This is a multi-threaded pipeline that applies 24 mathematical transformations to every generated base key. This allows testing not just one hypothesis, but an entire matrix of probabilities simultaneously.
Key pattern groups include:
- Bitwise Operations: Bit inversion (NOT), cyclic shifts (ROL/ROR), and XOR stitching. These methods identify keys affected by data distortion during network transmission or disk storage.
- Structural Deformations: “Endian Swap” (changing byte order) and “Nibble Swap” methods. These patterns target keys created in environments with different byte orders (Big-Endian vs Little-Endian), which often happened when porting code between different processor architectures.
- Advanced Cryptography: Utilizing “Modular Inverse” and “Lattice Mirror” strategies. These rely on the fundamental properties of the SECP256K1 elliptic curve, allowing the discovery of related keys through their geometric reflections.
- Magic Constants: The “Genesis XOR” pattern uses hashes of the first Bitcoin blocks as a mask. History shows that early developers often used this data in their experimental key generation scripts.
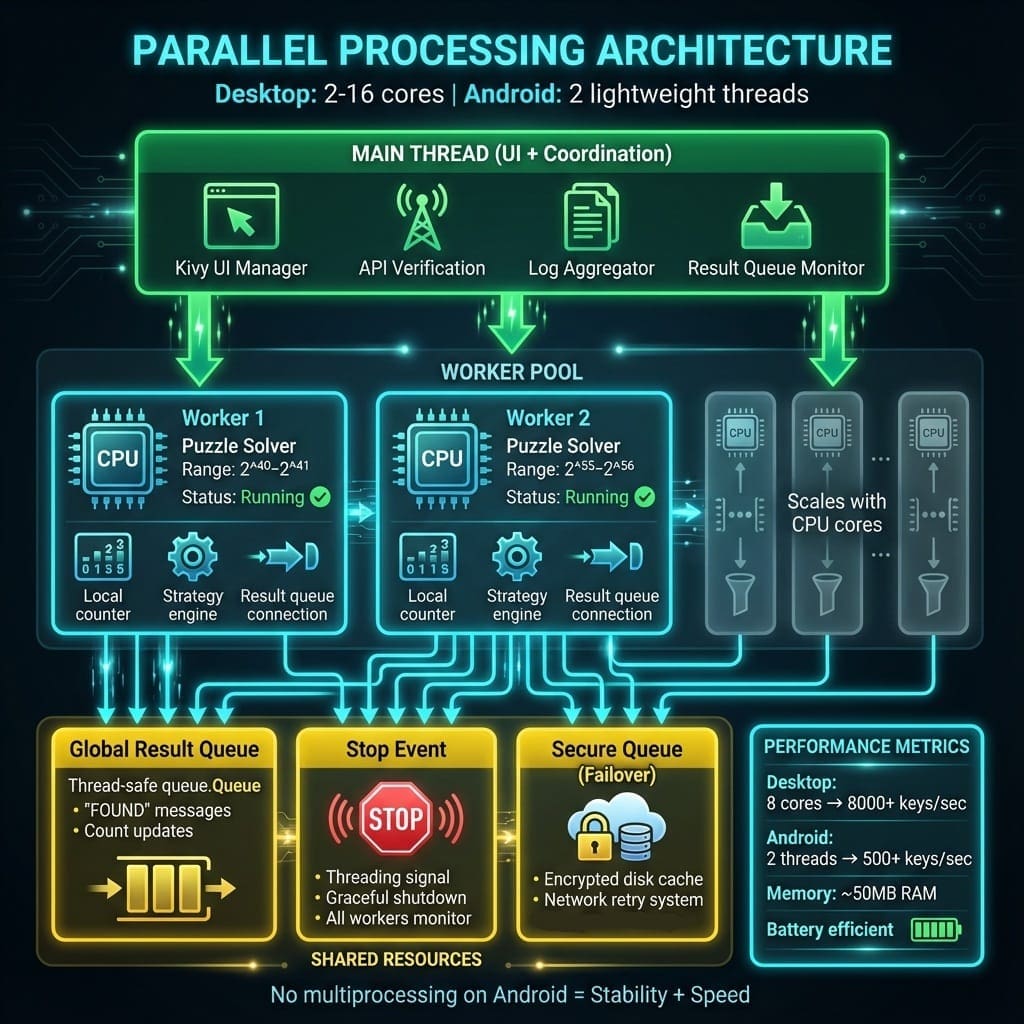
4. Liquid Flow Architecture: Speed and Scalability
The key search process in BTC Hunter is implemented through the highly efficient Liquid Flow pipeline. It minimizes delays between key generation and blockchain verification.
- Parallel Multi-Threading: The program dynamically distributes the load across all available processor cores (from 2 to 16 and more). Each thread operates independently, preventing memory resource contention.
- Hardware Optimization: The code is optimized for modern CPU instruction sets, allowing scanning speeds of several thousand keys per second on a standard home PC.
- Android Engine: A unique implementation on mobile devices uses a lightweight thread architecture, enabling “hunting” on smartphones without critical battery drain or overheating.
5. Four Vectors of Attack on the Key Space
The technical logic of BTC Hunter v2.4 is divided into four vectors, each targeting a specific class of vulnerabilities:
- Implementation Vector: Searching for errors in the code of specific wallets (Coding Errors), such as hardcoding parts of the key or incorrect memory buffer clearing.
- Mathematical Dependency Vector: Utilizing X and Y coordinates of public points to calculate the “missing” part of a private key via fast hash table lookup algorithms.
- Human Psychology Vector: Analyzing visual patterns and “Brainwallets,” where users chose keys based on phrases or visual sequences.
- Cross-Protocol Compatibility Vector: Checking every generated key against all four address types simultaneously (Legacy P2PKH, Compressed P2PKH, Nested Segwit P2SH, Native Segwit Bech32). One key — four chances for success.
6. Technical Verification via Blockchain API
The program does more than just generate keys; it performs industrial-grade balance verification. Instead of querying each address individually (which would lead to an immediate IP ban), BTC Hunter uses batch verification. Within a single API request, up to 40-50 addresses are checked simultaneously, accelerating the process by orders of magnitude and ensuring 24/7 system stability without the risk of being banned by blockchain nodes.
Conclusion: Science Against Chaos
The Bitcoin Private Key Finder — BTC Hunter project is a tool that elevates lost Bitcoin recovery from the realm of science fiction to applied data analysis. By harnessing the power of multi-threading, the unique Matrix Shotgun strategy, and a deep understanding of cryptographic flaws, the program offers a chance to reclaim assets that have lain dormant for decades.
For a deeper dive into technical documentation, system requirements, and to access the latest version of the software, visit the project’s official technical resource: