Identity and Access Management Market Scope and Overview
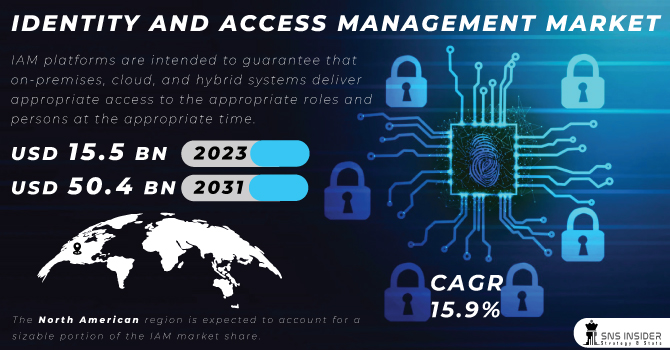
In an era where digital transformation is a driving force across industries, Identity and Access Management (IAM) has become a cornerstone of cybersecurity and operational efficiency. IAM systems are designed to ensure that the right individuals have access to the right resources at the right times, while protecting sensitive information from unauthorized access. With the increasing complexity of IT environments and the growing number of cyber threats, organizations are investing heavily in IAM solutions to secure their digital assets and comply with regulatory requirements. This report provides a detailed analysis of the Identity and Access Management Market, focusing on key players, market segmentation, growth drivers, and the overall strength of the market.
The Identity and Access Management (IAM) market revolves around technologies and practices that ensure the right individuals have the appropriate access to resources within an organization. IAM solutions encompass user authentication, authorization, and management to secure sensitive information and systems. As organizations face increasing cybersecurity threats and regulatory requirements, the demand for robust IAM solutions has grown. These systems help streamline user access processes, enhance security, and ensure compliance, making them crucial for protecting against data breaches and unauthorized access.
Competitive Analysis
The Identity and Access Management (IAM) market is characterized by intense competition, with several major players vying for market share. Leading companies include SecureAuth, EmpowerID, SAP, and OndIdentity, which offer a range of IAM solutions tailored to various organizational needs. Microsoft and IBM are prominent players, leveraging their extensive technology portfolios to provide integrated IAM solutions that address both on-premises and cloud-based requirements. Oracle and Salesforce are also key players, known for their robust IAM offerings that cater to enterprise-level needs.
CyberArk and Okta are recognized for their advanced security solutions and cloud-based IAM capabilities. FusionAuth, Avatier, and Beyond Identity contribute to the competitive landscape with innovative solutions that focus on specific aspects of IAM, such as password management and advanced authentication methods. The presence of these diverse players highlights the dynamic nature of the IAM market, where companies continually evolve their offerings to meet the growing and changing demands of organizations worldwide.
Identity and Access Management Market Segmentation
By Services
- User Provisioning: User provisioning involves creating and managing user accounts and their associated access rights across various systems. This service ensures that new employees or partners have the appropriate access from day one and that terminated employees are promptly removed from systems to prevent unauthorized access. Effective user provisioning helps streamline onboarding and offboarding processes, enhancing security and operational efficiency.
- Single Sign-On (SSO): Single Sign-On is a service that allows users to access multiple applications with a single set of login credentials. This simplifies the user experience by reducing the number of passwords users need to remember and manage. SSO improves productivity and enhances security by reducing the risk of password fatigue and related security issues.
- Access Management: Access management involves controlling and monitoring user access to various systems and resources based on predefined policies. This service ensures that users have access only to the resources they need to perform their roles, thereby minimizing the risk of unauthorized access and data breaches. Effective access management is crucial for maintaining the integrity and confidentiality of sensitive information.
- Multi-Factor Authentication (MFA): Multi-Factor Authentication adds an additional layer of security by requiring users to provide multiple forms of verification before gaining access. This could include something they know (password), something they have (smartphone), or something they are (biometrics). MFA significantly enhances security by making it more difficult for unauthorized individuals to gain access even if they have compromised one form of authentication.
- Password Management: Password management solutions help users create, store, and manage passwords securely. These solutions often include features such as password generation, secure storage, and automated password changes. Effective password management reduces the risk of weak or reused passwords, which are common vulnerabilities in cybersecurity.
- Directory Services: Directory services involve maintaining and managing directories that store information about users, devices, and resources within an organization. These services facilitate user authentication and authorization, enabling efficient management of user identities and access rights across various systems and applications.
- Governance and Compliance Management: Governance and compliance management ensures that IAM policies and practices comply with relevant regulations and industry standards. This includes monitoring and auditing access controls, managing policies and procedures, and generating reports for compliance audits. Effective governance and compliance management help organizations meet regulatory requirements and avoid potential legal and financial penalties.
By Deployment Mode
- Public: Public IAM solutions are hosted and managed by third-party service providers. These solutions offer scalability and cost-efficiency, making them suitable for organizations with varying needs and budgets. Public IAM solutions are often adopted by small to medium-sized enterprises (SMEs) that require flexible and affordable IAM options.
- Hybrid: Hybrid IAM solutions combine on-premises and cloud-based components, providing organizations with the flexibility to integrate existing infrastructure with cloud services. This deployment mode is ideal for organizations that need to balance security and compliance requirements with the benefits of cloud scalability and cost savings.
- Private: Private IAM solutions are deployed within an organization’s own infrastructure, offering greater control and customization. This deployment mode is typically chosen by large enterprises with stringent security and compliance requirements, where sensitive data and critical applications require heightened protection.
By Industry Verticals
- BFSI (Banking, Financial Services, and Insurance): In the BFSI sector, IAM solutions are critical for managing access to financial systems, protecting sensitive customer data, and ensuring compliance with regulatory requirements. IAM systems in this vertical focus on securing transactions, preventing fraud, and maintaining the integrity of financial operations.
- IT and Telecommunication: IAM solutions in the IT and telecommunication sector help manage access to IT systems, networks, and communication platforms. These solutions ensure that only authorized personnel can access critical infrastructure and sensitive data, supporting operational efficiency and security in a rapidly evolving technological landscape.
- Healthcare: In the healthcare industry, IAM solutions are essential for safeguarding patient information, complying with regulations such as HIPAA, and managing access to electronic health records (EHRs). IAM systems help healthcare organizations protect sensitive data, enhance patient privacy, and streamline access management processes.
- Media & Entertainment: IAM solutions in the media and entertainment sector address the need for secure access to digital content, intellectual property, and production systems. These solutions help manage user access to content distribution platforms, production tools, and other resources while protecting against unauthorized access and piracy.
- Retail: In the retail industry, IAM solutions are used to manage access to point-of-sale systems, customer data, and supply chain management systems. IAM systems help retailers ensure secure transactions, protect customer information, and streamline access to various retail operations.
- Education: IAM solutions in the education sector manage access to educational resources, student information systems, and administrative applications. These solutions support secure access for students, faculty, and staff, and facilitate compliance with data protection regulations.
- Others: The “Others” category encompasses a range of industry verticals, including government, manufacturing, and transportation. IAM solutions in these sectors are tailored to address specific security and access management needs, supporting the diverse requirements of various organizations.
Key Growth Drivers of the Identity and Access Management Market
Several factors are driving the growth of the Identity and Access Management market. Firstly, the increasing frequency and sophistication of cyberattacks are compelling organizations to invest in robust IAM solutions to protect their digital assets. The rise in regulatory requirements and compliance mandates is another significant driver, as organizations seek to ensure they meet industry standards and avoid penalties.
The growing adoption of cloud computing and the proliferation of mobile devices are also contributing to market growth. Cloud-based IAM solutions offer scalability and flexibility, while mobile device management and access control are becoming increasingly important in a mobile-first world. Additionally, the shift towards digital transformation and the need for seamless user experiences are driving demand for advanced IAM solutions that integrate with various applications and systems.
Strengths of the Identity and Access Management Market
The Identity and Access Management market benefits from several strengths that contribute to its growth and resilience. The market is characterized by a diverse range of solution providers, offering various products and services to meet the needs of different organizations. This diversity ensures that organizations can find IAM solutions tailored to their specific requirements, whether they are looking for cloud-based, on-premises, or hybrid solutions.
The continuous advancement of IAM technologies, such as artificial intelligence (AI) and machine learning (ML), enhances the capabilities of IAM systems, enabling more sophisticated threat detection, automated access management, and improved user experiences. The integration of IAM solutions with other security technologies, such as Security Information and Event Management (SIEM) and endpoint protection, further strengthens the market’s offerings and provides comprehensive security solutions.
Key Objectives of the Market Research Report
The market research report on Identity and Access Management aims to achieve several key objectives:
- Provide a comprehensive overview of the IAM market, including its size, growth trends, and key drivers.
- Analyze the competitive environment, highlighting major players, their strategies, and market positioning.
- Offer a detailed breakdown of the market by services, deployment mode, and industry verticals, including insights into each segment’s performance and trends.
- Identify and evaluate the factors driving market growth and their impact on the industry.
- Assess the strengths of the market and highlight opportunities for growth and innovation.
- Address potential challenges and risks facing the IAM market, such as regulatory changes and evolving cyber threats.
- Provide an overview of market dynamics and opportunities in different regions, including North America, Europe, Asia-Pacific, and others.
Conclusion
The Identity and Access Management market is a dynamic and rapidly evolving sector that plays a crucial role in securing digital environments and enabling efficient access management. With key players continuously innovating and expanding their service offerings, the market is well-positioned for growth. The increasing emphasis on cybersecurity, compliance, and digital transformation is driving demand for IAM solutions across various industries.
By understanding market segmentation, key growth drivers, and the strengths of the market, stakeholders can make informed decisions and strategically position themselves to capitalize on emerging opportunities. As the IAM landscape continues to evolve, organizations must stay ahead of the curve by adopting advanced IAM solutions that address their unique needs and challenges, ensuring robust security and operational efficiency in an increasingly complex digital world.
Table of Contents
- Introduction
- Industry Flowchart
- Research Methodology
- Market Dynamics
- Impact Analysis
- Impact of Ukraine-Russia war
- Impact of Economic Slowdown on Major Economies
- Value Chain Analysis
- Porter’s 5 Forces Model
- PEST Analysis
- Identity and Access Management Market Segmentation, Services
- Identity and Access Management Market Segmentation, by Deployment Mode
- Identity and Access Management Market Segmentation, by Industry Verticals
- Regional Analysis
- Company Profile
- Competitive Landscape
- USE Cases and Best Practices
- Conclusion
Contact Us:
Akash Anand – Head of Business Development & Strategy
info@snsinsider.com
Phone: +1-415-230-0044 (US) | +91-7798602273 (IND)
About Us
SNS Insider is one of the leading market research and consulting agencies that dominates the market research industry globally. Our company’s aim is to give clients the knowledge they require in order to function in changing circumstances. In order to give you current, accurate market data, consumer insights, and opinions so that you can make decisions with confidence, we employ a variety of techniques, including surveys, video talks, and focus groups around the world.
Read Our Other Reports:
Cloud Supply Chain Management Market Share
Smart Building Market Research
Network Security Firewall Market Overview
Virtual Data Room Market Statistics

