Every time you log into a website, show your ID at a bar, or apply for a loan, you are sharing sensitive data. To prove you are who you say you are, you typically have to hand over the “keys to the castle”—your password, your home address, or your exact date of birth.
This exchange creates a massive vulnerability. We constantly expose more information than is necessary to complete a transaction.
But what if you could prove a statement is true without revealing the data behind it? What if you could prove to a bouncer you are over 21 without letting them see your name or address? Or prove you have enough money for a transaction without revealing your bank balance?
This is the promise of Zero Knowledge Proofs (ZKPs). While the concept sounds like magic, it is based on complex cryptography that is rapidly moving from academic whiteboards to real-world applications. ZKPs are poised to redefine how we handle privacy, security, and scalability online.
What is a Zero Knowledge Proof?
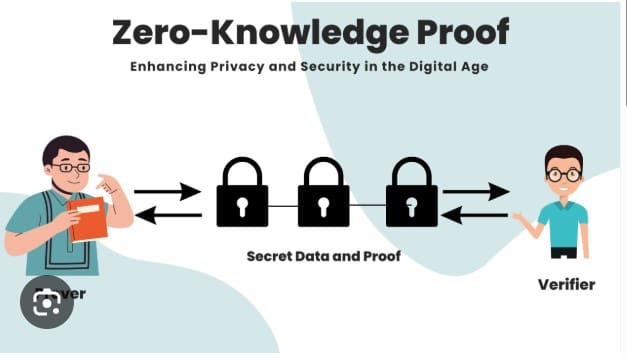
At its core, a Zero Knowledge Proof is a method where one party (the Prover) proves to another party (the Verifier) that a statement is true, without conveying any additional information apart from the fact that the statement is indeed true.
To be considered a valid ZKP, a protocol must satisfy three specific properties:
- Completeness: If the statement is true, an honest verifier will be convinced by an honest prover.
- Soundness: If the statement is false, a cheating prover cannot convince the verifier that it is true (except with a negligible probability).
- Zero-Knowledge: If the statement is true, the verifier learns nothing other than the fact that the statement is true. They do not learn the secret information.
The “Where’s Waldo” Analogy
Cryptography can be dense, so let’s use a simple analogy to visualize how this works.
Imagine you and a friend are looking at a “Where’s Waldo” book. You claim you have found Waldo. Your friend, the skeptic, doesn’t believe you. You want to prove you found him, but you don’t want to reveal his location because you want your friend to find him on their own later.
How do you prove you know where Waldo is without pointing to him on the page?
The Solution:
You take a large piece of cardboard that is much bigger than the book. You cut a small hole in the center of the cardboard. You place the cardboard over the book so that Waldo is visible through the hole, but the rest of the page (the context of his location) is covered.
The Result:
Your friend looks through the hole. They see Waldo.
- Proof: They now know for a fact that you found him.
- Zero Knowledge: They still have no idea where on the page he is located relative to the circus tent or the beach.
You have successfully proven your knowledge without revealing the secret itself.
How ZKPs Work Under the Hood
In a digital context, we aren’t using cardboard and books; we are using algorithms. The interaction usually involves a series of mathematical challenges.
- The Commitment: The Prover picks a secret number and uses it to generate a “commitment” (an encrypted value) sent to the Verifier.
- The Challenge: The Verifier sends a random question or mathematical challenge back to the Prover. This challenge can only be answered correctly if the Prover truly knows the secret.
- The Response: The Prover solves the challenge and sends the answer back.
- Verification: The Verifier checks the answer. If it’s correct, they gain confidence.
If they repeat this process multiple times, the statistical probability of the Prover guessing the right answers without knowing the secret drops to near zero.
Interactive vs. Non-Interactive Proofs
The method described above requires a back-and-forth conversation. This is known as an Interactive Zero Knowledge Proof. While effective, it isn’t efficient for things like blockchains, where a prover (like a user sending a transaction) and a verifier (the network) aren’t always online simultaneously.
This led to the development of Non-Interactive Zero Knowledge Proofs (niZKPs).
In this model, the Prover generates a single, bundled proof that can be verified by anyone at any time without further communication. This is the standard used in modern cryptocurrency and privacy tools. The two most common types you will encounter are:
- zk-SNARKs: (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge). These are small, fast to verify, and widely used. However, they usually require a “trusted setup”—a specific initial event to create the cryptographic keys.
- zk-STARKs: (Zero-Knowledge Scalable Transparent Argument of Knowledge). These do not require a trusted setup and are theoretically resistant to quantum computing attacks, but the proof sizes are generally larger than SNARKs.
Why Do We Need Zero Knowledge Proofs?
The implications of this technology extend far beyond just keeping secrets. They solve fundamental structural problems in our digital systems.
1. Privacy in Public Blockchains
Blockchains like Bitcoin and Ethereum are public ledgers. Anyone can see the sender, receiver, and amount of every transaction. ZKPs allow for privacy coins (like Zcash) and privacy layers where transaction validity is proven without revealing the details to the public.
2. Scalability (ZK-Rollups)
This is currently the biggest use case in the Ethereum ecosystem. Blockchains are slow because every node has to verify every transaction.
ZK-Rollups bundle thousands of transactions off-chain, generate a single cryptographic proof that all those transactions are valid, and then submit just that tiny proof to the main blockchain. This drastically reduces congestion and fees, making the network faster and cheaper.
3. Identity and Authentication
We currently rely on passwords, which are frequently stolen. ZKP protocols allow you to log in to a service by proving you know the password without actually sending the password across the network.
Furthermore, it allows for “Self-Sovereign Identity.” You could prove to a bank that your credit score is above 700 without giving them your full financial history, or prove citizenship for voting without revealing your identity to the poll worker.
Challenges and Limitations
Despite the hype, ZKPs are not a silver bullet—yet. There are significant hurdles to widespread adoption.
- Computational Intensity: Generating these proofs requires heavy mathematical lifting. It takes significantly more computing power and time to create a zero-knowledge proof than to simply sign a standard transaction. This can make them slow or expensive to generate on consumer hardware like mobile phones.
- Complexity: The mathematics involved is incredibly dense. This creates a high barrier to entry for developers. If a ZKP circuit is coded incorrectly, it could lead to vulnerabilities that are difficult to detect.
- The “Trusted Setup” Risk: As mentioned with zk-SNARKs, some protocols require an initial creation of keys. If the people who created those keys collude or don’t destroy the “toxic waste” (the initial data) properly, they could theoretically forge false proofs.
The Future of Private Verification
We are moving toward a world where data privacy is not just a policy choice, but a technological guarantee. Zero Knowledge Proofs provide the infrastructure for a society where transparency and privacy are no longer mutually exclusive.
In the near future, you might verify your income for an apartment rental, vote in a national election, or access medical records, all while revealing only the absolute minimum amount of information required.
The math is complex, but the outcome is simple: You reclaim ownership of your data.